Russia has always maintained it did not interfere in the 2016 US presidential elections, in spite of significant evidence that says otherwise. And Russia continues to deny any involvement in recent attacks on US targets that may represent an early assault on the incoming elections.
Microsoft has found evidence that Russian hackers that were linked to the Russian government in the past tried to target the websites of two right-wing US think tanks. Microsoft was able to thwart those attacks.
An unnamed Russian diplomatic source told Interfax (via Reuters) that “Microsoft is playing political games.”
“The (mid-term US) elections have not happened yet, but there are already allegations,” the person said, adding that Microsoft was acting like a prosecutor, rather than a private company.
Just a few hours ago, Microsoft detailed in a blog post the kind of attack it was able to prevent. What the company’s DCU unit was able to do after executing a court order was to seize some six domains that attackers could have used for early spear phishing attacks:
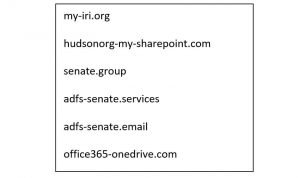
Broadening cyberthreats to both U.S. political parties make clear that the tech sector will need to do more to help protect the democratic process. Last week, Microsoft’s Digital Crimes Unit (DCU) successfully executed a court order to disrupt and transfer control of six internet domains created by a group widely associated with the Russian government and known as Strontium, or alternatively Fancy Bear or APT28. We have now used this approach 12 times in two years to shut down 84 fake websites associated with this group. Attackers want their attacks to look as realistic as possible, and they, therefore, create websites and URLs that look like sites their targeted victims would expect to receive email from or visit. The sites involved in last week’s order fit this description.
Here are the fake sites the hackers created, replicating actual sites, including a fake Office 365 OneDrive site:
The more prominent targets that can be easily tied to US politicians and elections include the International Republican Institute “which promotes democratic principles and is led by a notable board of directors, including six Republican senators and a leading senatorial candidate.”
A second domain mimicked the Hudson Institute, which hosts discussions on various topics, including cybersecurity.
Microsoft says it has no evidence any of the seized addresses were actually used in attacks, and that it hasn’t identified the actual targets. However, Microsoft expects these attacks to continue, and the company announced that it’d offer a free product called Microsoft AccountGuard to all candidates and campaign offices at every level, including federal, state and local. The technology includes state-of-the-art cybersecurity protection, and it’s bundled with Office 365.
The purpose of this fake websites is to trick unsuspecting users into entering their credentials, which attackers could then use to mount other attacks leading up to the mid-term elections.








