Preinstalled malware is definitely not one of the reasons why you purchased your current Android smartphone or tablet, but if you’re the owner of various ZTE and Archos, then you also have malware on board.
The news comes from Avast, which found an adware type of malware that simply loads ads in your browser. It’s not the most nefarious attack you could find on a smartphone, but with no known fix other than a sledgehammer, it’s certainly the most persistent.
Avast specifically named these manufacturers in an announcement, saying that most devices are not certified by Google. Several hundred models are affected, but most of them are tablets. And most of them are powered by MediaTek chips.
The adware’s name is called Cosiloon, and what it does is to create an ad over the webpage you might be loading in your browser. The adware has been active for some three years, and it’s difficult to remove, apparently, as it’s installed on the firmware level “and uses strong obfuscation.”
Avast identified some 18,000 devices infected by the malware in more than 100 countries, including Russia, Italy, Germany, the United Kingdom, Ukraine, Portugal, Venezuela, Greece, France, and Romania.
Google has also been notified of the issues, and it’s working to mitigate the issues, but even Google can’t deal with the apps as long as they’re preinstalled on the devices. Google has apparently reached out to developers to raise awareness on the matter.
Avast discovered these “dropper” apps inside the file system of apps preinstalled on a device. This variant is a passive app visible in the list of system applications under “settings.” These droppers can download a manifest from certain servers, which contains further instructions on what to download on the phone.
The dropper downloads a second app APK and installed in the device. Users can’t uninstall the droppers given that they’re built into the firmware.
A second dropper version is embedded in the SystemUI.apk, which is part of the Android OS, which makes it even harder to remove.
The payload that either dropper can install is apparently “heavily obfuscated and very complex.” It can even detect whether it’s used in an antivirus emulator, in which case it’ll hold back on its actions. If necessary, it can update itself by getting the appropriate files from a server.
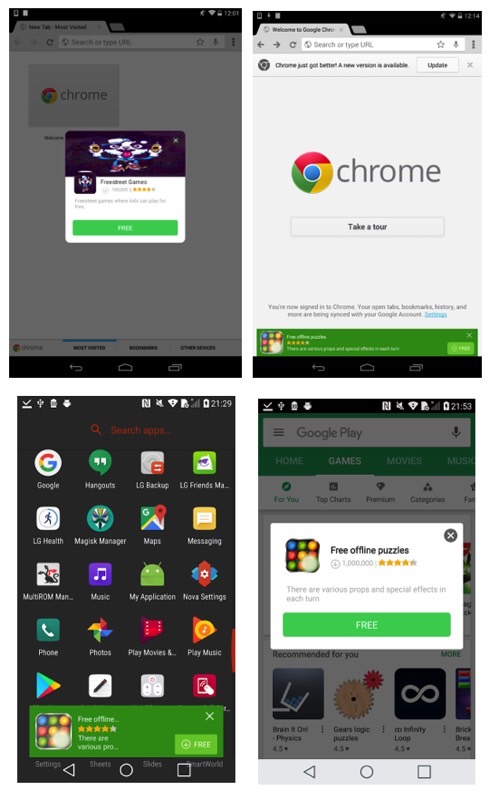
When activated, the payload will deliver ads to various apps and games. Needless to say, you should avoid clicking on any of those ads (see examples in the screenshots above).
Avast says it can detect the payload and uninstall it, but it can’t do anything about the dropper that’s built into the system. If you want to read more about its findings, check out this link. A list of affected devices is available here.
UPDATE: A previous version of this post included myPhone in the list of affected devices. Avast corrected its original report to remove the brand from the list.








