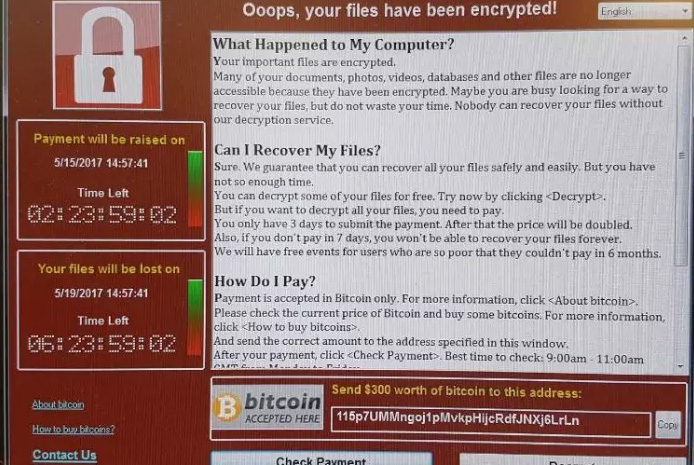
A new ransomware attack, modeled after the recent WannaCry exploit, has hit thousands of organizations and users worldwide. But according to a handful of security experts, it’s only the tip of the iceberg. The ransomware attack, which encrypts users’ files and demands a ransom to unlock them, could just be a test attack, or cover for more malicious damage being done by the virus.
““I’m willing to say with at least moderate confidence that this was a deliberate, malicious, destructive attack or perhaps a test disguised as ransomware. The best way to put it is that Petya’s payment infrastructure is a fecal theater,” security researcher Nicholas Weaver told KrebsOnSecurity.
His sentiments were echoed by “the grugq,” an anonymous security researcher who blogs about security issues. He highlights the same thing as Weaver, namely that the payment infrastructure for the virus is poorly designed.
Normally, ransomware viruses demand payment in Bitcoin to a Bitcoin account that is unique to every victim. That makes it harder to track the Bitcoin, or for researchers to work out the identity of the attackers.
Communication is normally done through the obfuscated Tor protocol, which relies on a distributed web of servers and is impossible for one organization to shut down. In this instance, however, the attackers had one single email address listed for communication. It was quickly shut down by Posteo, the German ISP responsible for the email account. That means that victims will not be able to communicate with the attackers to organize payment or receive decryption codes, effectively meaning any encrypted files will be lost forever, if backups aren’t available.
“If this well engineered and highly crafted worm was meant to generate revenue, this payment pipeline was possibly the worst of all options (short of “send a personal cheque to: Petya Payments, PO Box …”),” the grugq explains. It’s suspicious that such a well-designed piece of ransomware would have such a bad payment system — unless, of course, the aim was never to make money.
“This is definitely not designed to make money. This is designed to spread fast and cause damage, with a plausibly deniable cover of “ransomware.”, the grugq continues.
Weaver confirmed this to Krebs, saying that Petya “appears to have been well engineered to be destructive while masquerading as a ransomware strain.”
Attributing blame for cyberattacks is always difficult, but the high concentration of Ukranian victims — the attack was originally distributed through Ukranian tax software MeDoc — raises questions about potential Russian involvement.