- Tens of malicious Google Chrome Store add-ons that were downloaded more than 32 million times spied on browsing data and stole personal information, including credentials for various services.
- Google has removed the spyware add-ons from its store after researchers notified the company of the new threat.
- It’s unclear who was behind the attack or for what purpose, but the malicious extensions were sophisticated enough to avoid antivirus detection and to stop transmitting data when used over a more secure corporate network.
Chrome is one of Google’s most popular apps and the world’s most used internet browser. But that doesn’t necessarily make it the safest to use. A new report indicates that Google Chrome may have been spying on you and stealing sensitive data, and it’s all thanks to one of Chrome’s great features that wasn’t adequately supervised. Chrome lets you install all sorts of extensions that can make your life easier, but some of them can contain malicious code that would allow attackers to intercept browsing data. Google’s own security features and oversight should prevent such attacks on users at large in theory. In practice, researchers have discovered more than 70 malicious add-ons that were installed over 32 million times.
Google removed the add-ons last month from the Chrome Web Store once Awake Security informed them of the issues. But that can’t be good enough for the users who were actually convinced to install these malicious Chrome apps.
“When we are alerted of extensions in the Web Store that violate our policies, we take action and use those incidents as training material to improve our automated and manual analyses,” Google spokesman Scott Westover told Reuters.
This isn’t the first time when malicious add-ons were discovered in the Chrome Store. Google said in 2018 it would improve the security and increase human review, but that did not prevent the spyware that Awake Security to sneak past them.
In February, other researchers discovered a different malicious Chrome campaign that stole data from 1.7 million users. At the time, Google found 500 fraudulent extensions.
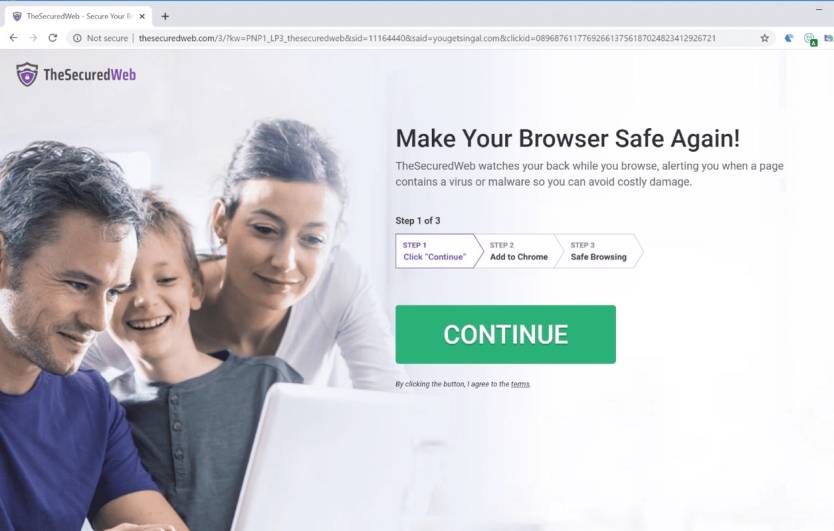
Reuters notes that most of the free extensions were supposed to warn users about questionable websites (example above) or allow them to convert files from one format to another. But what they actually did was to transfer browsing history data, including credentials to internal business tools.
The malicious add-ons were designed to avoid detection from antivirus companies and security software. On top of that, they were smart enough to check what type of connection was in use. The add-ons would turn on to steal data if somebody used the browser on a home computer, and send it to a series of websites to transmit the intercepted information. Should someone use a corporate network instead of a home one, the add-ons would behave differently. They would not send sensitive information or connect to malicious versions of websites.
“This shows how attackers can use extremely simple methods to hide, in this case, thousands of malicious domains,” Awake co-founder and chief scientist Golomb said. He added that based on the number of downloads, this is the most far-reaching malicious campaign targeting Chrome to date.
It’s unclear who was behind the sophisticated attacks, as the developers supplied fake contact information to Google when submitting the extensions.
The hackers used more than 15,000 domains, which were all purchased from Israeli registrar Galcomm. Awake researchers think Galcomm should have known what was happening, but the company’s owner Moshe Fogel told Reuters the company did nothing wrong, and it’s not involved in any way.
Fogel also said he had no record of the inquiries that Awake made in April and May. Reuters reports it sent him the list of suspect domains three times, but the exec never offered “a substantive response.” Galcomm has just over 26,000 registered domains in total, including the 15,000+ malicious ones.
You can read more about Awake’s findings at this link. If you think you may have been a victim, it’s time to revisit your Chrome add-ons and consider changing passwords to the various online services that you might be using.







