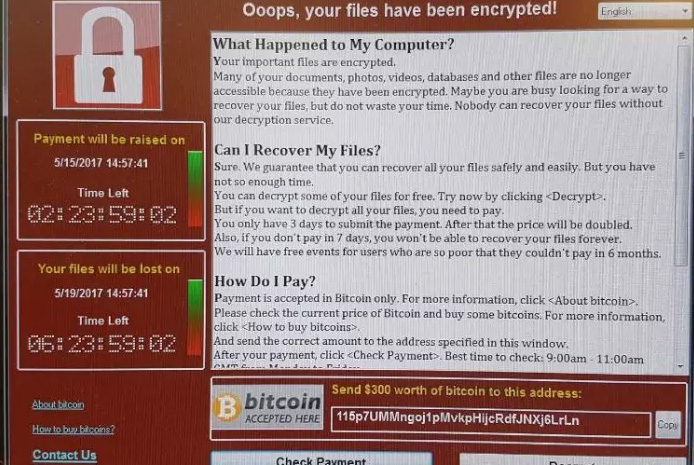
Earlier this year, a 23-year-old security researcher miraculously stopped a viral computer virus that was spreading to hundreds of thousands of Windows computers faster than anything else. The computers WannaCry crippled were not instantly saved, but Marcus Hutchins managed to prevent others PCs from getting the ransomware.
Now, the same security researcher is held by the FBI, as he’s accused of having created a rather dangerous banking malware a few years ago.
Called Kronos, and sold online in July 2014 for as much as $7,000, the malicious software was able to steal credentials and personally identifying information from infected computers. The data could then be used to access the online bank accounts of unsuspecting users.
What’s interesting about the software is that its creators said at the time that it could evade existing anti-virus software and that it could work with the latest versions of Internet Explorer, Firefox, and Chrome. Moreover, the virus would be able to alter forms on bank pages to add fields for additional information, including PIN codes, Wired reports.
Versions of Kronos were spotted in banking attacks as late as November 2016, when a security company discovered that the software was distributed via email attachments to organizations in various businesses, including financial services, hospitality, higher education, and healthcare.
It’s unclear at this time what Hutchins’s role was in the creation of Kronos. But the FBI believes he’s responsible for the program.
A second defendant is also included in the indictment, BBC, but the name has not been made public.
Hutchins could face 40 years in jail if found guilty, US cyber-attorney Tor Ekeland told BBC, but he added that the case did not name any victims of the Kronos attack.
The IBM researchers who found Kronos for sale in May 2014, and posted a translation of the advertisement used to sell it, as found on a Russian underground forum:
I present you a new banking Trojan
Compatible with 64 and 32bit rootkit Trojan is equipped with the tools to give you successful banking actions.Formgrabber: Works on Chrome, IE, FF in latest versions. Works on the majority of older versions as well. Steals logs from each website Webinjects: Works on latest Chrome, IE, FF, latest and majority of older versions. Injections are in Zeus config format, so it’s easy to transfer the config from one another.32 and 64bit Ring3 rootkit: The Trojan also has a ring 3 rootkit that defends it from other Trojans.
Proactive Bypass: The Trojan uses an undetected injection method to work in a secure process and bypass proactive anti-virus protections. Encrypted Communication: Connection between bot and panel is encrypted to protect against sniffers. Usermode Sandbox and rootkit bypass: The Trojan is able to bypass any hook in usermode functions which bypasses rootkits or sandboxes which use these hooks.
1000$ a week of testing. The server will be hosted only for you. You need just a domain or a payment including the domain fee. You’ll have full access to the C&C, without any limits or restrictions during test mode.7000$ Lifetime product license, free updates, and bug removals. New modules will not be free, and you will need to pay additionally. We accept Perfect Money, Bitcoin, WMZ, BTC-E.comCurrently the Trojan is written in its fullest. Next week we will have tests and bug fixing, then release. Pre-ordering the Trojan will give you a discount.