No One Is Safe: This Tiny $30 Device Can Break Into Your Car And Home
Not everyone wants to accept this simple truth, but that doesn't make it any less real: hackers outpace security advancements. When it comes to both online security and real-world security, hackers have already devised 10 new tools by the time security researchers come up with an effective way to block one old tool. As a result, no one is ever truly safe — and a new device recently shown off by a well-known security researcher is yet another example of just how vulnerable we really are.
DON'T MISS: Why do I still use Android?
Online and offline security expert Samy Kamkar took to Defcon 2015 to show off a tiny device he calls "Rolljam." The device is as shockingly simple as it is devious and brilliant, and it can be used to break into just about any car. Worse yet, it can even be used to break into a target's home.
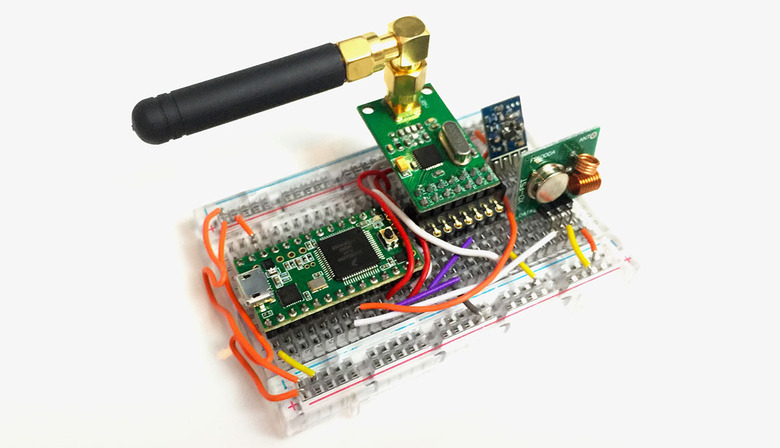
Rolljam is a tiny series of circuit boards with three in-built radios, Wired reports. It works by using two of the radios to jam the wireless signal sent out by a car's keyless entry remote, while the third radio reads the code that was transmitted by the remote, which is then stored on the device.
Keyless entry devices use a system of rolling codes to prevent hackers from stealing them wirelessly and reusing them at will. Once a code is used a single time, it cannot be used again — and therein lies the brilliance of the Rolljam device.
Since the device blocks the signal from a car's key fob while it is being transmitted, the unique code never reaches the owner's car. The next time he or she presses the unlock button, a new code will be transmitted and it will successfully unlock the car. But that first code was never actually used, so the Rolljam can then transmit it at a later time and it will successfully unlock the target car.
Kamkar's device was used to successfully unlock cars made by Nissan, Cadillac, Ford, Toyota, Lotus, Volkswagen and Chrysler, and it also worked perfectly with a number of garage door openers, potentially giving the user access to a target's home.
"This is throwing the gauntlet down and saying, 'here's proof this is a problem,'" says Kamkar. "My own car is fully susceptible to this attack. I don't think that's right when we know this is solvable." As Kamkar noted, systems like two-factor authentication use codes that automatically expire in a matter of seconds, and the same concept would render Rolljam completely ineffective.