These Fake Android File Manager Apps Steal Banking Logins
Android device owners beware — more malicious apps have been discovered on the Google Play store. Bitdefender's cybersecurity team says several fake Android file manager apps are infecting Android devices with the SharkBot banking malware. These fake apps are no longer available on the store, but they might still be on your phone. Screenshots of the store pages show that thousands of Android users downloaded these malicious apps.
As Bleeping Computer explains, SharkBot malware tries to steal bank accounts by displaying fake login forms on top of legitimate login prompts found in banking apps. If you input your username and password into the fake form, it will be sent to a hacker, who can then use it to infiltrate your account and steal your money.
In September, we warned about SharkBot malware disguised as phone cleaning apps. Now, the threat actors appear to have moved on to file manager apps. One such app (which isn't on Google Play anymore) was X-File Manager, with over 10,000 downloads.
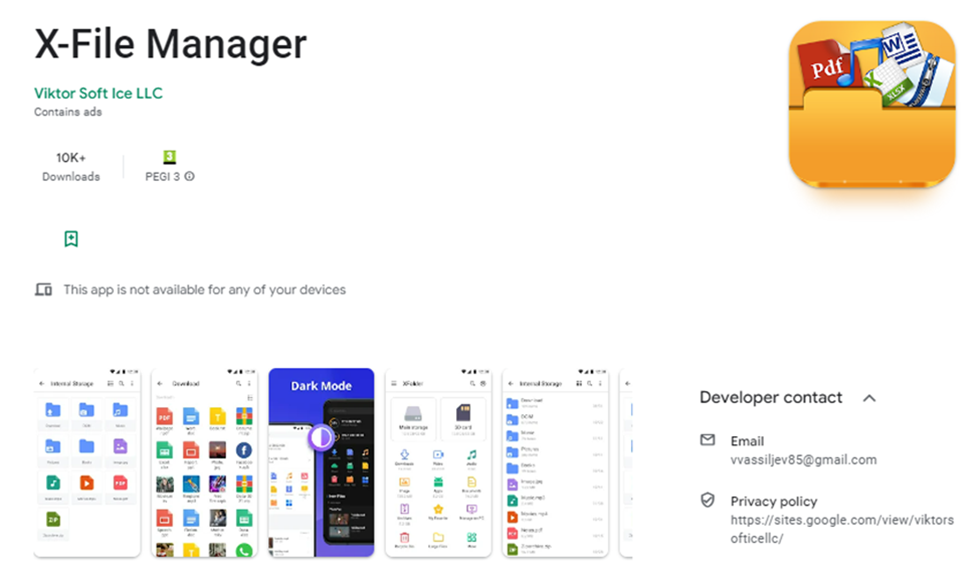
X-File Manager installs malware on Android devices.
Upon downloading the app, users shouldn't be suspicious. The app does ask for a bunch of invasive permissions, including reading and writing external storage, installing and deleting packages, and accessing account details. But this is a file management app. It makes sense that it would need more permissions than an average productivity app.
Eventually, the app downloads the malicious payload and prompts the user to install an update. In reality, the user is installing the SharkBot malware.
According to Bitdefender, this campaign is specifically targeting users in Great Britain and Ireland. If the app detects a SIM card from those regions, it will download the malware. The banking apps targeted by the campaign include Barclays, Bank of Ireland Mobile Banking, Santander Mobile Banking, and HSBC UK Mobile Banking.
Other apps Bitdefender claims were infecting Android devices include "FileVoyager," "Phone AID, Cleaner, Booster," and "LiteCleaner M." If you have any of these apps on your Android device, delete them as soon as you possibly can.
READ MORE: 4 dangerous Android malware apps discovered on Google Play
