Yet Again, Adware-Infected Android Apps Rack Up Millions Of Google Play Store Downloads
Researchers associated with ESET, a cybersecurity research company, have uncovered the latest variant of a scheme we've been reporting on different iterations of for a while now. It's the latest batch of adware-infected Android apps to have been discovered lurking in the Google Play Store — a total of 42, all of which seem to have since been booted from Google's app marketplace. But not, of course, before racking up millions of downloads.
The apps in question included titles like Ringtone Maker Pro and SaveInsta, both of which were downloaded some half a million times. As ESET security researcher Lukas Stefanko explains in a post detailing what the team uncovered, these kinds of apps tend to serve ads that take up a device's full screen randomly once they've been downloaded. And the adware-laden apps in questions employed some tricks to keep their secret purpose hidden for as long as possible.
While all that was happening, the apps were also quietly capturing data about the user's device that could be used later. The thing that appears to have allowed them to sneak into the Google Play Store is the apps' ability to check and see if they're being tested by the Play Store's security mechanisms. If the app thinks that's the case, the app won't let its adware payload be triggered, according to ESET.
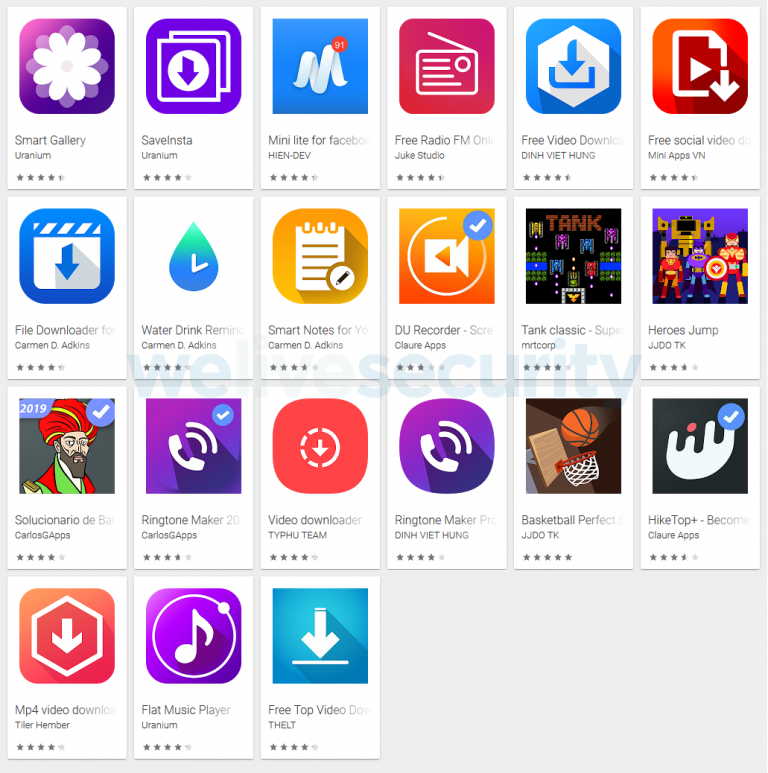
These, by the way, are the apps ESET says it reported to Google:
"Based solely on open-source intelligence, we were able to trace the developer of the ... adware and establish his identity and discover additional related adware-infected apps," Stefanko writes in his post. "Seeing that the developer did not take any measures to protect his identity, it seems likely that his intentions weren't dishonest at first — and this is also supported by the fact that not all his published apps contained unwanted ads.
"At some point in his Google Play 'career,' he apparently decided to increase his ad revenue by implementing adware functionality in his apps' code. The various stealth and resilience techniques implemented in the adware show us that the culprit was aware of the malicious nature of the added functionality and attempted to keep it hidden."
