Meet Chat, Another New Google Messaging Service That's Still Not As Good As Apple's iMessage
Ever since Apple rolled out iMessages, Google has been trying to catch up, but the company never managed to come up with an instant messaging app that was just as good, or secure, as Apple's.
Long-time Android fans have witnessed the SMS/instant messaging mess on Android, as Google rolled out plenty of apps over the years supposed to offer users better chatting experiences. But the company wasn't able to deliver anything close to an iMessage competitor. Until now?
Google Chat is supposedly the chat app that will bring the Android texting experience closer to iPhone, according to an in-depth The Verge report on the new app.
However, we'll tell you from the get-go, that Chat will not have one of the best features of iMessage. Apple's default iPhone texting app comes with end-to-end encryption for messages sent as iMessages. The app turns texts into regular SMS messages when they're sent to Android users, in which case they're handled by carriers rather than Apple's servers.
Google Chat is based on the RCS, or Rich Communication Services, a new standard for SMS texts. A whole bunch of carriers and device makers already support RCS messaging, and Google is working with all of them to bring RCS to Android as Chat. Apple is notably absent from that list. It'll be surprising if it decides to support RCS going forward, given its stance on user data privacy and security.
Because Chat will work via the infrastructure of mobile operators, which are more open to providing access to text messaging records to police, it won't be end-to-end encrypted. One other important reason for not encrypting it is Google's own needs. Google Assistant has to work inside the Chat app, and that means it needs to see the messages that are exchanged in it. It's just like Allo, the previous iMessage alternative from Google that the company is now dumping in favor of Chat.
One reason for carriers to hate iMessage is that it doesn't produce any sort of revenue for them. These texts are sent via the internet between iOS devices, so carriers can't tax them. Sure, you pay for the data, but iMessage is one of the mobile chat apps that started killing SMS a few years ago.
The politically correct answer for the lack of encryption and the need of carrier control is that Google wants to keep Android an open platform, which means it doesn't want to force a proprietary Chat experience on carriers and device makers. You know, like Apple did with iMessage. Google's Anil Sabharwal, who's overseeing the Chat project, explains it so:
We can't do it without these [carrier and OEM] partners. We don't believe in taking the approach that Apple does. We are fundamentally an open ecosystem. We believe in working with partners. We believe in working with our OEMs to be able to deliver a great experience.
That said, if you're okay with an iMessage-like experience without the encryption, then you can expect Chat to work on your Android devices at some point later this year. Or next year. There's no clear rollout because Chat functionality depends both on carrier and device support.
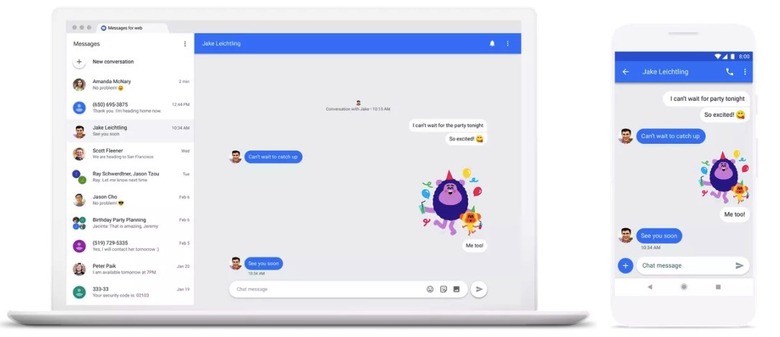
And yes, you can expect a desktop version of Chat to work on your computer. iMessage too works on both mobile and desktop computers.
You'll still have access to other encrypted chat apps on Android, including WhatsApp, Telegram, and Signal, although none of them will ever replace the default SMS app on your handset.
Check out The Verge's Chat preview video: